Last year, British hacker Kane Gamble was sentenced to two years in youth detention for targeting a number of top U.S. intelligence officials in what the judge described as “politically motivated cyber terrorism.”
The case highlighted how the Internet could be used by individuals or lone wolves, and even terrorist organizations, to attack what could perhaps be counted among the world's most secure intelligence networks and confidential national assets.
In 2014, when Gamble was all of 15, he had gained access to intelligence operations in Afghanistan and Iran by pretending to be then CIA chief John Brennan after hacking into his computers.
A year later, the Leicestershire-based British teen breached the FBI's intelligence database known as the Law Enforcement Enterprise Portal (Leap) by posing as the agency's then deputy director Mark Giuliano.
'Social engineering'

British hacker Kane Gamble in London, UK, on January 19, 2018. /AP Photo
British hacker Kane Gamble in London, UK, on January 19, 2018. /AP Photo
In all his hacks, Gamble successfully used the ploy of "social engineering” which translates into gathering publicly available information on the Internet to impersonate someone, and then use this fake identity to gain access to other databases from help desks, call centers, and other sources.
Gamble also hacked into the personal broadband of Jeh Johnson, the then U.S. Secretary of Homeland Security, and tapped his voicemails while also sending texts from his phone. He used this access to harass Johnson's family.
Gamble, who is now 19, later posted sensitive information from his exploits on Twitter and WikiLeaks, at times using the tag #FreePalestine and accusing the U.S. Government of “killing innocent people.”
His reign of “cyber terrorism” ended in February 2016, soon after he broke into the U.S. Department of Justice's network and accessed information on some 20,000 FBI employees and files of several sensitive cases, including the Deepwater Horizon Oil Spill.
This breach put the FBI and U.S. secret service in a tizzy, who immediately contacted the British police and got the teenager arrested.
Judge Charles Haddon-Cave, who read out the verdict against Gamble last April, described his actions as an "extremely nasty campaign of politically motivated cyber terrorism."
Rise of the lone wolves

Norwegian mass murderer Anders Behring Breivik makes a Nazi salute ahead of his appeal hearing at a court at the Telemark prison in Skien, Norway, on January 10, 2017. /VCG Photo
Norwegian mass murderer Anders Behring Breivik makes a Nazi salute ahead of his appeal hearing at a court at the Telemark prison in Skien, Norway, on January 10, 2017. /VCG Photo
While Gamble, apparently a Palestinian-sympathizer, operated alone from his Coalville apartment in northwest Leicestershire against what he believed were U.S. atrocities, his case nevertheless also showed how the Internet is increasingly being used by radicalized individuals and terrorist organizations to create havoc and spread their agenda.
“Internet has developed into a supportive medium for extremist and terrorist organizations, groups and individuals to spread their agenda and to communicate within the groups, and with their followers. It has led to emergence of innovative terrorist practices such as lone wolves on the Internet, narrowcasting on the Internet, online terror financing and terror through social media,” Afeera Firdous, research assistant at the Islamabad-based Center for International Strategic Studies (CISS), said in her study titled “Terrorist Threat on Internet: Current Global Response.”
“Terrorism perpetrated by individuals, known as lone wolves, is the fastest growing phenomenon of terrorism, online and on ground. Lone wolf terrorists are being hired, radicalized, educated and trained by others on different online platforms like Facebook, Twitter, chat room, YouTube, etc,” she said in her study.
There are complete online guides for aspirant lone wolves, Firdous noted, saying that such tutorials offer “anything from constructing a home-made bomb to maps and vicinity of the target.”
The Internet also offers a platform for individuals, who are otherwise reluctant about sharing their radical opinions in public, to find other compatible individuals on online forums and therefore exposing them to extremist ideologies and agendas.
In the most extreme cases, the lone wolves take it upon themselves to carry out physical terrorist attacks, as we witnessed in the cases of the 2010 Stockholm suicide bomber Taimour Abdul Wahab al Abdaly and the 2011 Norway attacker Anders Behring Breivik.
“An individual, lone wolf, is an open threat to the society who is radicalized through the Internet and planning assaults in silence,” according to Gabriel Weimann, author of several books on terrorism including “Terror on the Internet: the New Arena” (2006) and “Terror in Cyberspace: The Next Generation” (2015).
Terror groups use 'narrowcasting'

A 3D plastic representation of the logos of Twitter and YouTube is seen in front of an Islamic State flag in this photo illustration in Zenica, Bosnia and Herzegovina, on February 3, 2016. /VCG Photo
A 3D plastic representation of the logos of Twitter and YouTube is seen in front of an Islamic State flag in this photo illustration in Zenica, Bosnia and Herzegovina, on February 3, 2016. /VCG Photo
Meanwhile, the Internet has also become a key tool in the hands of organized terrorist networks. It has allowed terrorist organizations to freely and inexpensively spread their propaganda and ideology across the world, allowing them to recruit new members and coordinate global attacks while evading surveillance.
Al Qaeda and the Islamic State (ISIL) are believed to be the first known terrorist organizations to harness the power of the Internet and social media. Their well-organized online propaganda campaign has seen them recruit thousands of foreign fighters, including those from Europe, North America and Southeast Asia.
Of the 12,000 foreign fighters in IS during 2013-16, 3,000 belonged to Western countries, according to a report by the Lebanon-based strategic security and intelligence service institute, the Soufan Group.
Firdous attributed these successes to “narrowcasting,” which she described as “the spread of ideas and content limited to a particular set of audience.”
“In general, narrowcasting aims to target an explicit portion of the community based on values system, social inclinations, demographic characteristics, and sex and age,” she said, adding: “Terrorists have understood and recognized its significance in the Internet domain and, therefore, are using it effectively.”
The CISS researcher pointed out that terrorists' websites, blogs, magazines, and Facebook pages have lately been focusing on children and women. “ISIL and Al Qaeda have been using digital publications/booklets for women and teenagers, stories and online video-games for children as tools to target a large online audience,” she elaborated.
According to Australian expert on counter-terrorism Anthony Bergin, terrorists and extremists use youth-dominated online forums such as Twitter, Facebook, and Myspace as a tool for propaganda and recruitment “in the same way a pedophile might look at those sites to potentially groom would-be victims.”
'Coordinated counter-strategy needed'
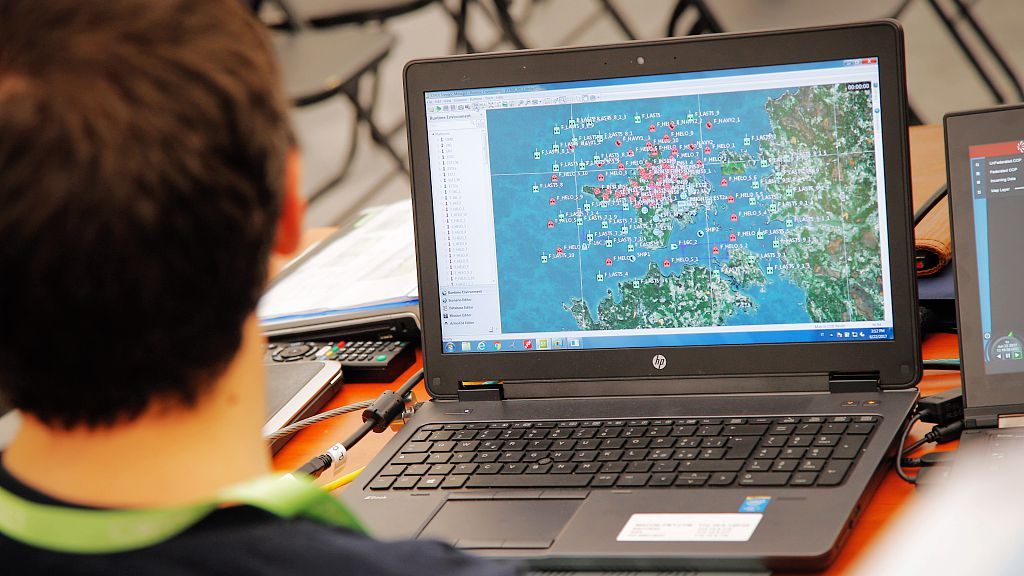
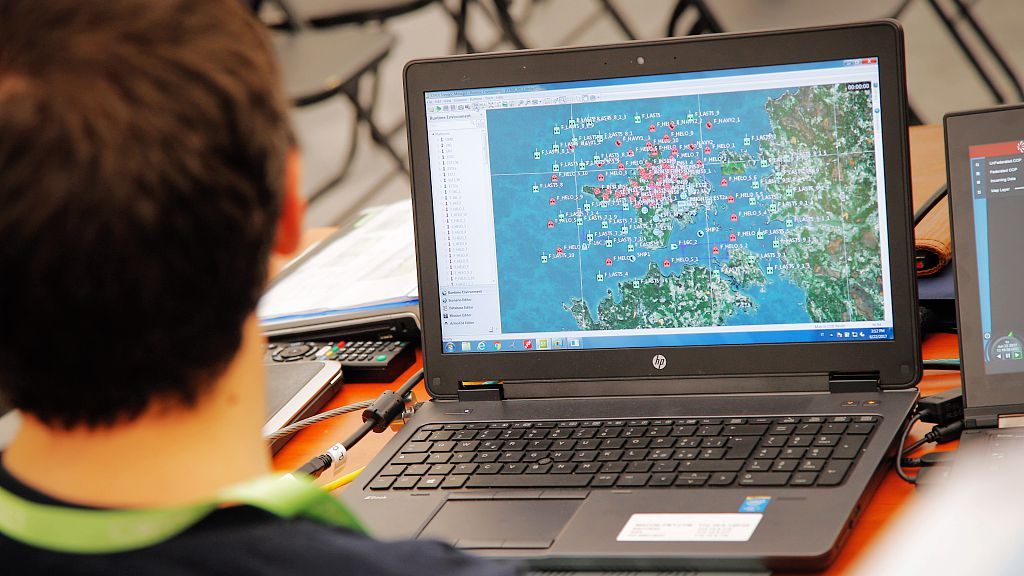
Exercises on cyberwarfare and security are seen taking place during the NATO CWIX interoperability exercise in Bydgoszcz, Poland, on June 22, 2017. /VCG Photo
Exercises on cyberwarfare and security are seen taking place during the NATO CWIX interoperability exercise in Bydgoszcz, Poland, on June 22, 2017. /VCG Photo
Firdous, however, makes a subtle distinction between “cyber terrorism” and “terrorist activities on the Internet.”
She described cyber terrorism as the use of computer network tools to hack into, crash or stop the critical national intelligence/infrastructure that could threaten a government and its civilian population, which is what Gamble did while targeting U.S. officials.
Whereas “terrorist activities on the Internet” usually involves spreading propaganda, fundraising, recruitment or planning, on various online platforms, which may at times also incite a lone wolf attack.
Explaining these distinctions, Firdous noted in her study that “there is not a single reported incident of cyber-attack or cyberterrorism against any country or government by terrorists” as yet, but warned that “with technological advancements and funds available to them (terrorists) such attacks cannot be ruled out in the future.”
To deal with the formidable threat of terrorists' presence on the Internet, Firdous recommended a coordinated approach between states, international organizations, IT and social media firms.
“Countering the menace of terrorism in cyberspace demands a comprehensive and finely tuned coordinated strategy in order to effectively deal with this threat,” she concluded.
'Outpacing physical attacks'

A person claiming to speak for activist hacker group Anonymous is seen issuing a warning through a video circulated online against the Singapore government's Internet licensing rules on November 1, 2013. /VCG Photo
A person claiming to speak for activist hacker group Anonymous is seen issuing a warning through a video circulated online against the Singapore government's Internet licensing rules on November 1, 2013. /VCG Photo
Meanwhile, in light of increasing cases of data breaches and information loss on the Internet, another study suggested that cyber-attacks are outpacing physical terror attacks among far-left groups and can cause greater destruction.
According to the paper published in the Terrorism and Political Violence journal and authored by Thomas Holt, professor at Michigan State University (MSU), the high-profile nature of the Internet - on which the ideological groups can manipulate traffic - is the ideal platform to attack.
The ideologically motivated attacks are devised to have an emotional and economic impact on groups that go against their beliefs. "Little work has been done around the use of the Internet as an attack space," Holt said.
"The bottom line is that these attacks are happening and they're overlooked. If we don't get a handle understanding them now, we won't fully understand the scope of the threats today and how to prevent larger mobilization efforts in the future."
To understand these attacks, Holt analyzed the scope, growth and impact of ideological cyber terrorist incidents from far-left groups, such as the Animal Liberation Front, Earth Liberation Front and the hacker conglomerate group, Anonymous.
These groups do not necessarily want to physically harm humans; rather, they are motivated by animal and environmental activism and feel passionate about attacking companies, organizations and government entities that go against their beliefs, Holt explained in the paper.
Holt's research also examined physical and cyber terror attacks committed by these far-left groups between 2000 and 2015 in the U.S., UK and Canada.
"These groups might strike domestically, but their damage on the web can be widespread and a concurrent risk for companies and consumers alike. It could be even greater," Holt said.
(Cover: Exercises on cyberwarfare and security are seen taking place during the NATO CWIX interoperability exercise in Bydgoszcz, Poland, on June 22, 2017. /VCG Photo)
(With input from IANS)