The three-day Pwn2Own 2017 World Hacking Contest has just finished. Qihoo's 360 Security team from China ranked first among the competitors with a total score of 63, receiving the “Master of Pwn” championship cup.
Pwn2Own, hosted by the Pentagon's network security service Zero Day Initiative (ZDI), is a worldwide computer hacking contest held annually at the CanSecWest Applied Security Conference in Vancouver, Canada. Pwn2Own 2017 is held from March 14 to 17.
The scale this year is the largest ever since the game began in 2007, with the largest number of registrations, the most entries and the highest prizes in history.

360 Security team. /360 Photo
Teams from the US, Germany, China and more participated in the game, aiming to hack the latest products from Microsoft, Google, Apple, Adobe, VMware and other technology companies. Contestants are challenged to exploit widely used software and mobile devices with previously unknown vulnerabilities.
The 360 Security team successfully exploited MacOS, Safari, Adobe Reader, Adobe Flash and Windows 10 during the first two days. On the last day, it chose to challenge the so-called "hardest in history" serial hacking, and they managed to take down Microsoft Edge and escape a virtual machine VMware to boot in only 90 seconds, achieving a score of 27, the highest in history on a single entry.
Microsoft Edge is a type confusion in the Windows kernel, and an uninitialized buffer in VMware Workstation for a complete virtual machine escape.
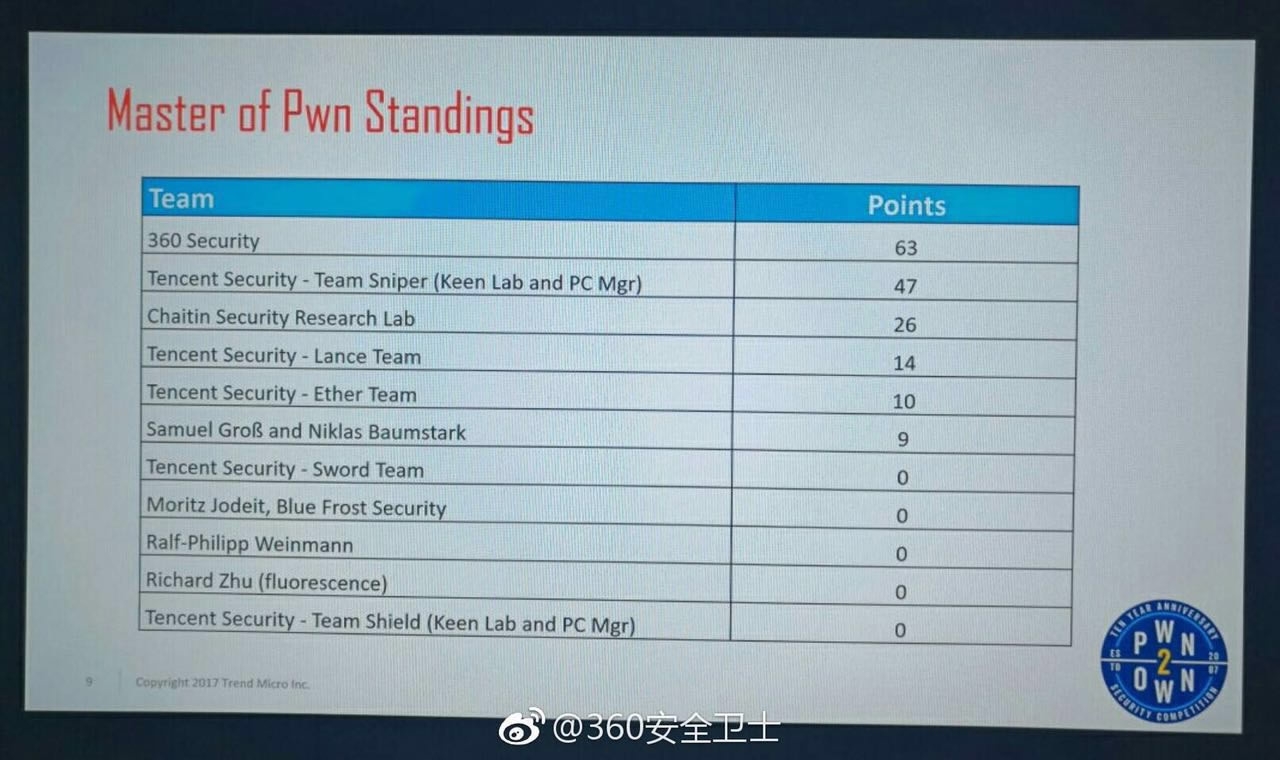
List of standing ranked by total scores received after day three. /360 Photo
Hacking contests have long been dominated by Western teams, but Chinese teams start to outperform in recent years. According to ZDI, the 360 Security team has been rewarded with a sum of more than 280,000 US dollars. The two other Chinese teams sent from Tencent Security and Chaitin Security received second and third place in the race.
All purchased bugs were privately disclosed to the vendors. Pwn2Own will continue working with them as they develop security patches.
The battle between cyber attack and defensive activities is endless, and only through constant innovation and improvements can experts explore the most effective security solutions.
8530km